Automated FPGA Verification and Debugging
Hardware simulations on FPGAs run more than three orders of magnitude faster than software simulations, but with much lower visibility into the circuit under test ...
Microsoft Research
FPGA IMPLEMENTATIONS OF THE HUMMINGBIRD CRYPTOGRAPHIC ALGORITHM
Hummingbird is a new ultra-lightweight cryptographic algorithm targeted for resource-constrained devices like RFID tags, smart cards, and wireless sensor ...
VERILOG COURSE TEAM
EL6453 - Final Project - Rijndael AES256 Encryption/Decryption on Spartan6 FPGA
Final project for NYU graduate course EL6453 - Advances in Reconfigurable Systems ***PLEASE NOTE: I no longer have the source code used for this project.
psciotto
COSIC seminar "Challenges in Real-world 'Secure' Cryptographic Hardware..." (Elif Bilge Kavun)
COSIC seminar – Challenges in Real-world “Secure” Cryptographic Hardware Implementations – Elif Bilge Kavun (The University of Sheffield) Physical attacks ...
COSIC - Computer Security and Industrial Cryptography
2. HAMS: Rationale behind an FPGA-based implementation
NECSTLab
Programming Reconfigurable Devices via FPGA Regions & Device Tree Overlays A User View Benchmark on…
Programming Reconfigurable Devices via FPGA Regions & Device Tree Overlays A User View Benchmark on a Declarative Reconfiguration Framework by ...
FOSDEM
Run-Time Reconfigurable CPU Interlays for Building Flexible Arm SoCs - Raul Garcia
Interlays are tiny reconfigurable fine-grained fabrics embedded into hardened CPUs to allow reconfigurable instruction set extensions. Their purpose is to ...
Arm Research
Signal Ratchet, a cryptographic technique, implemented in Lisp, by Ron Garret (lightning talk)
Bay Area Lisp and Scheme Meetup http://balisp.org/ Sat 4 Mar 2017 Hacker Dojo Santa Clara, CA Abstract Ron described his implementation, in Common Lisp, ...
Arthur Gleckler
Xilinx Zinq Ultrascale+: using a fast board interconnect to get 16Gb+ RDMA link between FPGAs
This video shows the AXIOM software layers, and the cluster setup. Basically, we are able to distribute computational nodes on various embedded boards by ...
Paolo Gai
NSDI '18 - Approximating Fair Queueing on Reconfigurable Switches
Naveen Kr. Sharma, University of Washington Congestion control today is predominantly achieved via end-to-end mechanisms with little support from the ...
USENIX
SoK: Understanding the Prevailing Security Vulnerabilities in TrustZone-Assisted TEE Systems
SoK: Understanding the Prevailing Security Vulnerabilities in TrustZone-Assisted TEE Systems—David Cerdeira, Nuno Santos, Pedro Fonseca, Sandro Pinto ...
IEEE Symposium on Security and Privacy
Cryptographic engineering
If you find our videos helpful you can support us by buying something from amazon. https://www.amazon.com/?tag=wiki-audio-20 Cryptographic engineering ...
WikiAudio
On the Difficulty of FSM based Hardware Obfuscation
Paper by Marc Fyrbiak, Sebastian Wallat, Jonathan Déchelotte, Nils Albartus, Sinan Böcker, Russell Tessier, Christof Paar, presented at CHES 2018.
TheIACR
Multiplex graph analysis with GraphBLAS
by Gabor Szarnyas At: FOSDEM 2019 https://video.fosdem.org/2019/H.1308/graph_multiplex_analysis_graphblas.webm Introduction Graph analysis workloads ...
FOSDEM
SDAccel Development Environment Demonstration
This video demonstrates the SDAccel development environment for acceleration using a standard X86_64 workstation containing an Alpha data ADM-PCIE-7V3 ...
XilinxInc
ClickNP: Highly Flexible and High Performance Network Processing with.. (SIGCOMM 2016)
ClickNP: Highly Flexible and High Performance Network Processing with Reconfigurable Hardware SIGCOMM 2016 Bojie Li Kun Tan Layong (Larry) Luo ...
Research in Science and Technology
Christopher Monroe, Quantum Information Science
"Quantum Information Science" Christopher Monroe, Distinguished University of Maryland Physics Professor & Bice Seci-Zorn Professor International ...
APS Physics
Implementation of Backpropagation Algorithm in Reconfigurable Hardware
We are providing a Final year IEEE project solution & Implementation with in short time. If anyone need a Details Please Contact us Mail: ...
SD Pro Engineering Solutions Pvt Ltd
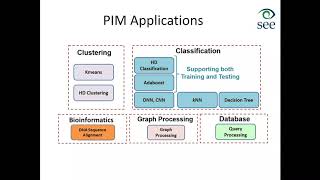
Prof. Tajana Simunic Rosing, Learning & Acceleration in loT Systems
Learning & Acceleration in IoT Systems With the emergence of the Internet of Things, devices will generate massive data streams demanding services that pose ...
Samsung Strategy & Innovation Center
A High-Speed FPGA Implementation of an RSD-Based ECC Processor
In this paper, an exportable application-specific instruction-set elliptic curve cryptography processor based on redundant signed digit representation is proposed.
Nxfee Innovation - Semiconductors
SDC 2017-Heterogeneous Multi-Processing for SW-Defined Multi-Tiered Stor Arch.. Ulrich Langenbach
Download Presentation: ...
SNIAVideo
Faculty Summit 2016 - How to Keep your Genome Secret
Over the last 10 years, the cost of sequencing the human genome has come down to around $1000 per person. Human genomic data is a gold-mine of ...
Microsoft Research
USENIX Enigma 2018 - Some Thoughts on Deep Learning and Infosec
Jeremy Howard, fast.ai and USF If you want to be accepted into the ML hipster clique, just say the magic words: "deep learning is over-hyped," and watch those ...
USENIX Enigma Conference
TEARDOWN 2019: Measuring embedded machine learning
Talk by Alasdair Allan While machine learning is traditionally associated with heavy-duty, power-hungry processors, the future of machine learning is on the ...
Crowd Supply
Michael Bernstein on A Unified Theory of Garbage Collection
Meetup: http://www.meetup.com/papers-we-love/events/163406212/ Audio: ...
PapersWeLove
Optimised Multiplication Architectures for Accelerating Fully Homomorphic Encryption (0916)
Large integer multiplication is a major performance bottleneck in fully homomorphic encryption (FHE) schemes over the integers. In this paper two optimised ...
ieeeComputerSociety
Ceph Scale-out Storage
In this video from the MSST 2017 Mass Storage Conference, Greg Tucker from Intel presents: Ceph Scale-out Storage. "Ceph is an open-source, unified, ...
RichReport
HC27-S1: Internet of Things
Session 1, Hot Chips 27 (2015), Monday, August 24, 2015. PULP: A Parallel Ultra-Low-Power Platform for Next Generation IoT Applications Davide Rossi(1), ...
hotchipsvideos
SDC 2017 - A New Key-value Data Store For Heterogeneous Storage Architecture - Brien Porter
Downloand Presentation: ...
SNIAVideo
Computer Science Colloquium February 18, 2010 - John Davis, Microsoft Research, Mountain View
John Davis, Microsoft Research, Mountain View BEE3: Silly Putty for Computer Scientists! Parallel computing for the masses has arrived. Unfortunately, software ...
CSUSonoma
Hedging Public Key Encryption in the Real World
Paper by Alexandra Boldyreva and Christopher Patton and Thomas Shrimpton, presented at Crypto 2017.
TheIACR
Philip Sibson: Integrated Silicon Photonics for Quantum Key Distribution
QCrypt 2016, the 6th International Conference on Quantum Cryptography, held in Washington, DC, Sept. 12-16, 2016. Web site: http://2016.qcrypt.net/
QuICS
APPSEC Cali 2018 - A Tour of API Underprotection
Abstract : Effective API protection is a growing concern, reflecting the popularity of RESTful Web APIs and richer front-end clients which stress current security ...
OWASP
Some Thoughts About Concurrency by Ivan Sutherland, Visiting Scientist at Portland State University
Our industry has grown up with a sequential model of computing, evolved to husband the logic associated with a few vacuum tubes. Now we must struggle to ...
USENIX
Why Design Must Change: Rethinking Digital Design -- Prof. Mark Horowitz, Stanford
Design is so expensive we can't afford to spend it on creating a single chip. Working out the interactions in a complex design is challenging and costs a lot of ...
Technion
How to Hack Radios: RF Physical Layers - Matt Knight and Marc Newlin at 44CON 2017 - Workshop
How to Hack Radios: Hands-On with RF Physical Layers - Presented by: Matt Knight and Marc Newlin at 44CON 2017 The Age of the Radio is upon us: wireless ...
44CON Information Security Conference
HC31-S8: Packaging and Security
Session 8, Hot Chips 31 (2019), Tuesday, August 20, 2019. Lakefield: Hybrid Cores in a Three Dimensional Package Sanjeev Khushu & Wilfred Gomes, Intel ...
hotchipsvideos
Post quantum digital signature with OQRNG (optical quantum random number generator) at DefCamp 2019
DefCamp is the most important conference on Hacking & Information Security in Central and Eastern Europe, bringing hands-on talks about the latest research ...
DefCamp
Introduction to Jetson Edge Devices - Cakes and Tensors
March 14th Cakes and Tensors Meetup.
Cakes & Tensors
FPGA Accelerated Computing Using AWS F1 Instances (121671)
The availability of FPGA instances on AWS, combined with improved cloud-based FPGA programming tools, provides researchers, application developers, and ...
Amazon Web Services
Customizing the Computational Capabilities of Processors
Consumers will always demand more performance from their computer systems. Real-time ray tracing and speech recognition are just two of the many ...
Microsoft Research
Intelligent Hardware Technologies Workshop: Neal Gershenfeld
Quest Workshop on Intelligent Hardware Technologies 10 Years Out "Keynote: Embodying AI" Neal Gershenfeld.
MIT Quest for Intelligence