USENIX Security '19 - The CrossPath Attack: Disrupting the SDN Control Channel via Shared Links
The CrossPath Attack: Disrupting the SDN Control Channel via Shared Links Jiahao Cao, Tsinghua University Software-Defined Networking (SDN) enables ...
USENIX
SF18US - 21: sFlow: Theory & practice of a sampling technology (Simone Mainardi)
The title of this class is: "sFlow: Theory & practice of a sampling technology and its analysis with Wireshark" and was taught by Simone Mainardi. This was ...
SharkFest Wireshark Developer and User Conference
Tailai Wen: ADTK: An open-source Python toolkit for anomaly detection in... | PyData Austin 2019
"ADTK is an open-source Python toolkit for unsupervised/rule-based time series anomaly detection. Focusing on building practical models in IoT environments, ...
PyData
Five Steps to Finding Your Cost Effective Level Solution, a Lesman Webinar
In this webinar, Mark Klee of Siemens talks to our customers about updates to level measurement technology that can improve your process results and reduce ...
Lesman Instrument Company
Anomaly Detection with IBM Tealeaf - Think 2019
When you're monitoring the sites or apps you rely on to drive business, it's the anomalies you want to know about, and now. Whether you get a spike or dip in ...
Acoustic
Anomaly Detection Real World Scenarios Approaches and Live Implementation
Detecting anomalous patterns in data can lead to significant actionable insights in a wide variety of application domains, such as fraud detection, network traffic ...
Impetus Technologies
NASA ARSET: Calculation of Precipitation Statistics Using IMERG, Part 1/3
Advanced Webinar: Applications of GPM IMERG Reanalysis for Assessing Extreme Dry and Wet Periods This session will provide a brief overview of IMERG ...
NASA Video
Riverbed Network Performance Management: The Power of Visibility
Through a broad spectrum of data sources, Riverbed's NPM offers complete visibility on network performance and security issues, ranging from on-prem ...
Tech Field Day
R&S Thirty-Five: 5G NR in the context of industrial apllications
Industrial IoT and non-public networks are important buzzwords in the 5G community. This presentation examines the technical components in 3GPP Release ...
Rohde Schwarz
Measure Matters Episode 1: Machine Learning
In a new series, Analytics Advocates Krista Seiden and Louis Gray will present live from Google headquarters in Mountain View. In episode one, the pair will ...
Google Analytics
Open Source Data Management for Industry 4.0
Continuously improving factory operations is of critical importance to manufacturers. Consider the facts: the total cost of poor quality amounts to a staggering ...
DataWorks Summit
Evaluating Network Traffic Analysis Systems – Requirements and Challenges
Network Traffic Analysis is emerging as an important new tool in the info security arsenal. While there is much marketing hype in this area, there has been a lack ...
Awake Security
Detection & Response: Building Effective SOC Operations
Tithirat Siripattanalert, Chief Information Security Office and Chief Data Officer at True Digital Group Our day concludes with an insider's view of how to effectively ...
RSA Conference
Web Performance Anomaly Detection with Google Analytics
If you are using Google Analytics, then you have a powerful anomaly detection engine at your disposal... and it can be easily configured to help you monitor the ...
Google Developers
Network Security and Visibility through NetFlow
With the rise of disruptive forces such as cloud computing and mobile technology, the enterprise network has become larger and more complex than ever before.
Cisco Stealthwatch
AWS re:Invent 2018: [REPEAT 1] AIOps: Steps Towards Autonomous Operations (DEV301-R1)
In this session, learn how to architect a predictive and preventative remediation solution for your applications and infrastructure resources. We show you how to ...
Amazon Web Services
Barefoot Networks Data Plane Telemetry and Deep Insight
Accurate data-plane streaming telemetry and INT are becoming highly popular network monitoring techniques to gain the right level of visibility for business ...
Tech Field Day
ManageEngine Webinar: Plugging Network Security Holes using NetFlow
With networks becoming bigger, faster and much more complex than ever before, the first element to take a hit is network security. This webinar discusses the ...
ManageEngine
AWS New York Summit 2018 - Threat Detection and Mitigation at Scale on AWS (SID301)
Learn more about AWS at - https://amzn.to/2n7GMdW. Organizations are using machine learning (ML) to address a host of business challenges, from product ...
Amazon Web Services
Tobias Kuhn, Nakul Selvaraj: Real-Time Monitoring of Distributed Systems
Instrumentation has seen explosive adoption on the cloud in recent years. With the rise of micro-services we are now in an era where we measure the most ...
PyData
Check_MK Conference #4 - Analysing Netflow with ntopng
The 4th Check_MK conference took place May 2-4, 2018 in the Munich, Germany. The yearly event brings together the Check_MK community with the product ...
Checkmk
Nana SHATASHVILI - Generalized Beltrami-Bernoulli Flow Model...
Generalized Beltrami-Bernoulli Flow Model for Astrophysical Disk-Jet Structure Formation In the vicinity of a massive object of various scales (ranging from ...
Institut des Hautes Études Scientifiques (IHÉS)
Using Automated Network Detection & Response to Visualize Malicious IT Events Within Power Systems
This webinar featured Gene Stevens, co-founder and chief technology officer of ProtectWise, on how the proliferation of Internet of Things devices, Internet ...
NREL Learning
Building a Data-Driven Business - Snehal Antani, CTO, Splunk Inc. (Full Presentation)
This video discusses how data is leveraged to solve critical problems, improve efficiencies, and optimize security in real time. Watch this video to learn: • How to ...
Splunk
Real-time Processing with Flink for Machine Learning at Netflix - Elliot Chow
Real-time Processing with Flink for Machine Learning at Netflix Machine learning plays a critical role in providing a great Netflix member experience. It is used to ...
Flink Forward
HTM Models for Adelaide Arterial Traffic Flow - Jonathan Mackenzie
2015 HTM Challenge Application Submission (1st place winner).
Numenta
Huawei Global ISP Summit 2020 Online
Stay tuned for the #Huawei #ISPSummit2020 to explore a range of keynote speeches, solution demonstrations, examples of best business practice, & alongside ...
Huawei Enterprise
Cybersecurity Law and Policy: What Are the Top Issues for 2019?
What are the top cybersecurity issues for 2019? Panelists discuss these topics. Panelists include: Ari Schwartz, the Managing Director of Cybersecurity Services ...
Duke University School of Law
Cardiopulmonary Bypass Emergencies - Part 1
A Department of Cardiovascular Surgery Grand Rounds from the Icahn School of Medicine at Mount Sinai presented by Percy Boateng, MD. At the end of this ...
Icahn School of Medicine
Data Science in Cyber-Security and Related Statistical Challenges
Data science techniques have an important role to play in the next generation of cyber-security defenses. Inside a typical enterprise computer network, a number ...
Microsoft Research
Master Series | An Introduction to IoT for Network Engineers
From Cisco Live 2020, Barcelona - Master Series with Tim Szigeti. The Master Series offers a unique opportunity to meet and engage with Cisco's top speakers ...
Cisco Live Europe
Enhanced Java Flight Recorder at Alibaba
https://developer.oracle.com/
Oracle Developers
Mining Anomalies in Network-Wide Flow Data
Speakers: Mark Crovella, Boston University. Christophe Diot, Thomson Paris Research. Anukool Lakhina, Boston University Network operators are routinely ...
TeamNANOG
How Pokémon Secures Data for Hundreds of Millions of Users with Sumo Logic
Learn more about AWS Shared Responsibility Model at – https://amzn.to/2Mkifkv Watch this webinar to learn how Pokémon leveraged security analytics and ...
Amazon Web Services
Threat Detection and Remediation in the Cloud
Learn more about AWS at – https://amzn.to/2EMC0vl This session provides an overview of the latest developments in AWS threat detection and remediation.
Amazon Web Services
SolarWinds How Netpath Works with Chris O'Brien
Chris O'Brien, Product Manager at SolarWinds, answers some questions about how specifically NetPath works. The origins of the tool was based on traceroute, ...
Tech Field Day
Autonomous cars: Science, technology, and policy - Part 2
On July 25 at the Brookings Institution hosted a full-day conference on how connecting vehicles to smart infrastructure will transform the future of transportation.
Brookings Institution
Web Performance Optimization (WPO) and Web Front-end Engineering with Dynatrace
Dynatrace helps web front-end engineers to learn more about how end users are leveraging their web applications. Dynatrace indicates performance hot spots ...
Dynatrace
Online Perf Clinic - Diagnosing and Boosting Java Application Performance with Dynatrace
Java Applications tend to be scattered, and it is not always easy to diagnose performance issues. In this session, Wayne Segar, Dynatrace Solution Consultant, ...
Dynatrace
Full Stack Monitoring of your Atlassian Stack using Dynatrace
How do you effectively monitor the health of your Atlassian ecosystem and easily troubleshoot issues? Dynatrace is a recommended monitoring tools in ...
Dynatrace
Lessons from an Outbreak Investigation
This Lessons from an Outbreak Investigation: Improving Medication Preparation, Use, and Other Infection Control Practices in Outpatient Oncology Clinics ...
Centers for Disease Control and Prevention (CDC)
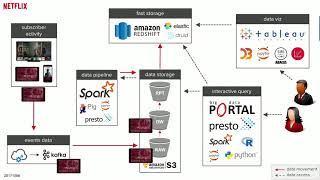
Netflix: A series of unfortunate events: Delivering high-quality analytics
"Netflix is a data-driven entertainment company, where analytics are extensively used to make informed decisions on every aspect of the business. As such ...
Tableau Software