Information Security Awareness | Training For Employees
Use this #template video: https://vynd.ly/3kccOlo to teach employees why information security is important and share best practices for avoiding data breaches.
Vyond
Information Security Analysts Career Video
JOB TITLE: Information Security Analysts OCCUPATION DESCRIPTION: Plan, implement, upgrade, or monitor security measures for the protection of computer ...
CareerOneStop
The Five Laws of Cybersecurity | Nick Espinosa | TEDxFondduLac
An expert in cybersecurity and network infrastructure, Nick Espinosa has consulted with clients ranging from small businesses up to the Fortune 100 level.
TEDx Talks
Information Security Awareness - Basic Training
Information security is paramount in today's technical environment. With the number and cost of cyber attacks, a business should not ignore information security.
PhishingBox
The difference between Cybersecurity and Information Security
Cybersecurity is a growing and rapidly changing field, and it is crucial that the central concepts that frame and define this increasingly pervasive field are ...
PECB
A Day In The Life Of A Cyber Security Specialist (Government Contractor)
Got a question? Drop it in the comments below! Become a YouTube member - https://www.youtube.com/channel/UC3sccPO4v8YqCTn8sezZGTw/join ...
DC CyberSec
Getting Into Cyber Security: 5 Skills You NEED to Learn in 2020
Thinking of getting into cyber security? Learn the most important skills you need for a beginner to be successful. With all the technical resources out there, it can ...
Cyberspatial
Cyber Security Fundamentals | Difference between cyber security and information security | 2020
In this Video i have explained 3 important concepts i.e. 1- What is an Information ? 2- What is cyber security 3- What is information security ...
Master Spark
An Introduction to Cybersecurity Careers
Developed for grades K-12, this module explains the cybersecurity skills shortage and encourages students to pursue a career in this growing field. It tackles ...
Infosec
What is Information Assurance vs Information Security vs Cyber Security?
What is the difference between Information Assurance (IA), Information Security (InfoSec) and Cyber Security? Make sure to subscribe so you don't miss new ...
Jon Good
What is ISO 27001? | A Brief Summary of the Standard
What is ISO 27001? A summary of the ISO 27001 information security standard. Learn about the ISO/IEC 27001:2013 standard and how an ISO ...
IT Governance Ltd
Cyber Security Full Course for Beginner
In this complete cyber security course you will learn everything you need in order to understand cyber security in depth. You will learn all the terminology related ...
My CS
Information Security Management - Key Concepts
Information Security Management - Key Concepts Lecture By: Mr. Shakthi Swaroop, Tutorials Point India Private Limited.
Tutorials Point (India) Ltd.
What is Information Security (InfoSec) | Buzzword
Information security, or InfoSec, is a common buzzword described by protecting a company's data to ensure its confidentiality, integrity and availability. These 3 ...
Impact My Biz
How Israel Rules The World Of Cyber Security | VICE on HBO
U.S. intelligence agencies accuse Russia of hacking the 2016 presidential election, a Ben Ferguson travels to Tel Aviv to find out how Israel is on its way to ...
VICE News
InfoSec vs. Cyber Security: There is a difference?
We hear the terms "information security" and "cyber security" bandied about. What do they man? How similar are they?
Kenyon Mau
Introduction to Cybersecurity
See this entire course on the Intro to Cybersecurity playlist. https://cbt.gg/2DEq4L6 Ready for the Cybersecurity quiz? Take it here. https://cbt.gg/2DyZeFg The ...
CBT Nuggets
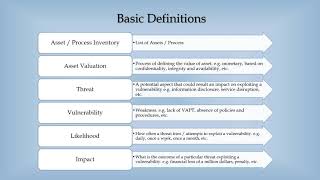
IT / Information Security Risk Management With Examples
This lecture is the part one of series for the IT / Information Security Risk Management. The video is good for students preparing for exams and interviews.
Ali Qureshi
Meet Security Engineers at Google
As a Security Engineer, you help protect network boundaries, keep computer systems and network devices hardened against attacks and provide security ...
Life at Google
The FUTURE of Information Security Engineers - Cisco Security Automation (DNA CENTER)
This video was sponsored by Cisco. Learn more about network programmability with Intent-Based Networking: http://cs.co/6001DvutX Check out the Cisco DNA ...
NetworkChuck
What is Cyber Security? | Introduction to Cyber Security | Cyber Security Training | Edureka
Edureka CompTIA Security+ Training: https://bit.ly/3nxeVRl This Edureka video on "What is Cyber Security" gives an introduction to the Cyber Security world and ...
edureka!
What is Cyber Security With Full Information? – [Hindi] – Quick Support
WhatisCyberSecurity #QuickSupport #Innovation What is Cyber Security With Full Information? – [Hindi] – Quick Support. Cyber security के बारे में तो आप ...
Quick Support
The Business of Cyber Security
You see hacks and data breaches on the news all the time. Target, Yahoo, eBay, and Sony are just some of the major companies where millions of records have ...
Fox5NY
Introduction To Cyber Security | Cyber Security Training For Beginners | CyberSecurity | Simplilearn
This Cyber Security training for beginners video covers all the basics that a beginner needs to know to get started with Cyber Security. It includes - what is Cyber ...
Simplilearn
Information Security || Characteristics Of Information || Lecture in Urdu/Hindi
Whaat is Information Security? What are the Characteristics of Information? Network Security..
Focus Group
4 Most Difficult IT Security Certifications
Start your free week with CBT Nuggets. https://cbt.gg/2LZhF9F Asher McClennahan from CBT Nuggets' Learning Content team answers a frequently asked ...
CBT Nuggets
Cybersecurity Frameworks | Information Security Tutorial | Cyber Security Course | 2020
Cybersecurity frameworks, Information security management framework course. Cyber security course for implementing security frameworks and certification ...
CybIT Cyber Security
Your Human Firewall – The Answer to the Cyber Security Problem | Rob May | TEDxWoking
Personal data is a precious commodity but sometimes we can share too much? Rob thinks we need to develop our human firewall in an age where some much ...
TEDx Talks
Cyber Security Full Course - Learn Cyber Security In 8 Hours | Cyber Security Training |Simplilearn
With the increase in global digital data, there is an increase in the number of cyberattacks too. Hence, businesses and individuals must secure their data, and for ...
Simplilearn
Information Security Risk Management Framework, what is it? Information Security Tutorial
This is the final stage in implementing your information security project - from the four-part beginners tutorial guide video series - focusing on how we manage ...
Best Practice
Firewalls and Network Security - Information Security Lesson #7 of 12
Dr. Soper discusses firewalls and network security. Topics covered include network vulnerabilities, port scanning, network segmentation, firewall security ...
Dr. Daniel Soper
Cybersecurity Fundamentals | Understanding Cybersecurity Basics | Cybersecurity Course | Edureka
Edureka CompTIA Security+ Certification Training: https://bit.ly/3nxeVRl This Edureka video on "Cybersecurity Fundamentals" will introduce you to the world of ...
edureka!
Lecture, Week 1, Intro to Information Assurance and Security
This is the first of five lectures I wrote and recorded for one of the classes I facilitate at the University of Phoenix. In this lecture, I discuss the basics of security and ...
Tom Olzak
Chief Information Security Officer Strategies 2021 (CXOTalk #670)
How do major financial institutions manage their enterprise security strategies and innovation in 2021? We talk with Dr. Alissa Abdullah, Mastercard's Deputy ...
CXOTALK
Cybersecurity: Crash Course Computer Science #31
Cybersecurity is a set of techniques to protect the secrecy, integrity, and availability of computer systems and data against threats. In today's episode, we're ...
CrashCourse
Information security | Episode 1
Do you know how hackers use USB, phising and social engineering to access and steal your information? In this section we meet the hacker Anna who reveals ...
Saab
The future of cyber security | FT
Around the world, cyber crime is on the rise. By 2050, smart cities and homes will be the norm. Your fridge will tell a drone to pick up fresh milk when you run out ...
Financial Times
Information security. How close to paranoia? | Martynas Savickas | TEDxMRU
Martynas is the total expert on information security. With more than 12 years of experience in information security and data privacy both in private and public ...
TEDx Talks
Information Security Specialist
Join us and help us protect our critical IT assets! You will assess and identify security gaps in our technology and solutions to prepare protection concepts and ...
Siemens
Webinar: Mikko Hypponen - Cyber Security and COVID-19
Business cyber security landscape has changed fast because of COVID-19. Organizations face new kinds of challenges due to uncertainty, the remote workforce ...
F-Secure
A day in the life of IT security
Find out how IT security take back control of the endpoint in this animation Learn more about Endpoint Control, the issues affecting organisations and how you ...
Kaspersky
Information Security—Before & After Public-Key Cryptography
[Recorded Jan 26, 2005] Whitfield Diffie, a key figure in the discovery of public-key cryptography, traces the growth of information security through the 20th ...
Computer History Museum