Introduction - Information Systems Security and Design
No End-of-Semester Project, instead there will be a Term Paper.
ICS 4
Secure Design Principles (CISSP Free by Skillset.com)
This Secure Design Principles training video is part of the CISSP FREE training course from Skillset.com (https://www.skillset.com/certifications/cissp). Skillset ...
Skillset
ICS 4203 Information Systems Security Design - Lecture 1
Lecture 1: Fundamentals of Information Systems Security.
Raj Gami
What is an Information System? (Examples of Information Systems)
Micheal talks about what is an information system and why they are so important. Store & Protect Your Passwords & Secrets with NordLocker: ...
Honest Careers
Become an Information System Security Engineer
Sign up for free courses! http://convocourses.com check us out here: http://www.nist80037rmf.com/ http://instagram.com/convocourses ...
ConvoCourses
Information Security Analysts Career Video
JOB TITLE: Information Security Analysts OCCUPATION DESCRIPTION: Plan, implement, upgrade, or monitor security measures for the protection of computer ...
CareerOneStop
The BEST Technology Degrees
This video is going to be about the best technology degrees available out there. SUBSCRIBE HERE: ...
Shane Hummus - The Success GPS
Information Systems Security Chapter 1
Information Systems Security Chapter 1.
ITSY 1300 Fundament Information Security
Security by design: What information handled by the system should not be disclosed and to whom?
To take advantage of emerging trends in both technology and cyberspace, businesses need to manage risks in ways beyond those traditionally handled by the ...
The Art Of Service
Basics for building a System Security Plan - SSP
Building a System Security Plan is a process that includes multiple variables. TechnologyMilestones can help. Check out our SSP services at ...
Jeffrey Lush
Learn Application Security in 5 Minutes | EC-Council | CASE
This video introduces you to the key skills needed for the Application Security Domain. For most organizations, software and applications determine their ...
EC Council
Security Architecture And Design | CISSP Training Videos
CISSP Certification Training: ...
Simplilearn
Lecture 2 - Information Systems Security and Design (Fundamentals)
ICS 4
What jobs are in Information Systems (2020)
Micheal talks about what tier of jobs you can get in Information Systems and how much they typically earn. Get Surfshark VPN at ...
Honest Careers
CS17: Security Architecture & Design | Secure Hardware Architecture |Secure software architecture
Download Handwritten Notes of all subjects by the following link: https://www.instamojo.com/universityacademy Join our official Telegram Channel by the ...
University Academy
Information Systems Security Special Topic Webinar: Reverse Engineering (12/18/2012)
UCI Division of Continuing Education
Lecture 4 - Information Systems Security and Design (28 - April - 2020)
ICS 4
Google Cloud Storage - Building Systems with Security by Design and Default (Cloud Next '18)
Learn about all the differentiated security primitives of Google Cloud's planet scale blob Storage service which you can leverage to build systems with security by ...
Google Cloud Platform
Webinar: How to implement an information security management system
mplementing an ISMS based on the best-practice guidance set out by ISO 27001 and ISO 27002 delivers numerous benefits, including reducing your risk of a ...
IT Governance Ltd
Information Technology Program at SUNY Canton
The Information Technology (IT) curriculum introduces the student to computer systems, networks, and communications. This academic program is appropriate ...
SUNY Canton
Secure by Design - Security Principles for the Working Architect - Eoin Woods [ACCU 2019]
Security #dataprotection #ACCUConf Security is an ever more important topic for system designers. As our world becomes digital, today's safely-hidden back ...
ACCU Conference
Information Systems Security Special Topic Webinar: Secure Systems (2/28/2012)
UCI Division of Continuing Education
Security Design CISA #2 (Certified Information System Auditors)
This Channel only for education purpose we do not support for illegal activity. If you are doing perform any illegal activity it's your responsibility Certified ...
DEKHAINDIA
ISSAP (Information Systems Security Architecture Professional) Training by SecureNinja
This is an overview of SecureNinja's ISSAP training and certification bootcamp. More information on the ISSAP Course can be found at ...
SecureNinjaTV
Google Cloud Storage - Building Systems with Security by Design and Default (Next Rewind '18)
Learn about all the differentiated security primitives of Google Cloud's planet scale blob Storage service which you can leverage to build systems with security by ...
Google Cloud Platform
CISA Training Video | Process of Auditing Information Systems - Part 1
CISA Training Video: The Process of Auditing Information Systems Domain 1 from CISA accounts you 21% of the exam and it talks about, how to conduct an ...
Simplilearn
Data Flow Diagrams - What is DFD? Data Flow Diagram Symbols and More
A data flow diagram, also known as DFD, helps you visualize how data is processed by or "flows through" a system in terms of inputs and outputs. This is ...
SmartDraw
Cyber Security In 7 Minutes | What Is Cyber Security: How It Works? | Cyber Security | Simplilearn
This short animated video on Cyber Security will explain what is Cyber Security, why Cyber Security, how Cyber Security works, who is a Cyber Security expert, ...
Simplilearn
System security
Explains what system security is and its relationship with other dependability attributes.
Ian Sommerville
Certified Information Systems Security Professional (CISSP)
The University of Fairfax invites you to a live presentation of our online Certified Information Systems Security Professional (CISSP) webinar presented by ...
University of Fairfax
ITIL Information Security Management, Part 3 Security Management Information System
This is the third video in the series on ITIL Information Security Management discussing Information Systems. This is a Process in the Service Design lifecycle ...
Jeffrey Tefertiller
Enterprise Information Systems Security
Worldskills Russia
Security Goals : Confidentiality,Integrity,Availability Explained in Hindi
GOOD NEWS FOR COMPUTER ENGINEERS INTRODUCING 5 MINUTES ENGINEERING SUBJECT :- Discrete Mathematics (DM) Theory Of ...
5 Minutes Engineering
Management Information System in Hindi Urdu LECTURE 01
For all lecture slides you can download form following website http://virtualcomsat.com Don't forget to subscribe my channel Management Information System in ...
Virtual Comsats
CompTIA CySA+ Security Architecture
Start your free week with CBT Nuggets. https://cbt.gg/2LZhF9F In this video, Keith Barker covers the incident response objectives that form the core of CompTIA's ...
CBT Nuggets
Occupational Video - Information Systems Consultant
Information systems consultants analyze, design and develop information systems business solutions and provide advice on a wide range of information ...
alisWebsite
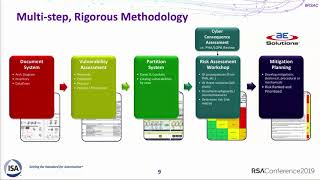
Safety Systems Are the New Target: Design Security Using Safety Methods
Marty Edwards, Director of Strategic Initiatives, International Society of Automation (ISA) Triton/Trisis/Hatman shows that industrial control safety systems are the ...
RSA Conference
CISSP: Certified Information Systems Security Professional Labs
uCertify
Information System Security & Control(Part-02)|Cyber Crime|Basic Principles of Information Security
Information security controls are measures taken to reduce information security risks such as information systems breaches, data theft, and unauthorized ...
ALL IN ONE FOR U ONLY
System Security Evaluation Models on Common Criteria (CISSP Free by Skillset.com)
This System Security Evaluation Models on Common Criteria video is part of the CISSP FREE training course from Skillset.com ...
Skillset
Cyber Security Full Course for Beginner
In this complete cyber security course you will learn everything you need in order to understand cyber security in depth. You will learn all the terminology related ...
My CS
2010-04-21 CERIAS - The role of System Security Engineering in the engineering lifecycle
Recorded: 04/21/2010 CERIAS Security Seminar at Purdue University The role of System Security Engineering in the engineering lifecycle Stephen Dill, ...
Purdue CERIAS