Windows Virtual Desktop updates for admins (2020)
See the admin-focused updates to Windows Virtual Desktop for the first half of 2020. Starting with the brand new Windows Virtual Desktop admin center, we'll ...
Microsoft Mechanics
What’s new in Microsoft Endpoint Manager: Part 2
Learn about the latest features in Microsoft Endpoint Manager and what's coming on the roadmap. In Part 2 we will focus on mobility management and endpoint ...
Microsoft 365
Azure security expert series: Cloud security with Ann Johnson
Please fast forward to 2:00 to watch the start of Ann Johnson's session. Welcome to the Azure Security Expert Series! Watch Ann Johnson, Corporate VP of ...
Microsoft Azure
Introduction to jBPM | jBPM Components | jBPM Architecture | jBPM Tutorial | Intellipaat
This jBPM online video helps you to learn following topics: 00:43 - jbpm suite key components 05:25 - jbpm architecture 06:28 - jbpm.org 20:19 - jbpm quiz If ...
Intellipaat
A Planned Methodology for Forensically Sound IR in Office 365 - SANS DFIR Summit 2018
A planned methodology for developing and implementing a forensically sound incident response plan in Microsoft's Office 365 cloud environment must be ...
SANS Digital Forensics and Incident Response
Building Robust Production Data Pipelines with Databricks Delta
Most data practitioners grapple with data quality issues and data pipeline complexities—it's the bane of their existence. Data engineers, in particular, strive to ...
Databricks
Hyperspace: An Indexing Subsystem for Apache Spark
At Microsoft, we store datasets (both from internal teams and external customers) ranging from a few GBs to 100s of PBs in our data lake. The scope of analytics ...
Databricks
Next.js: The React Framework - JS Monthly - July 2019
Next.js: The React Framework // Tim Neutkens - Zeit 63% of npm users are using React. Making it the most popular JavaScript framework ever. React is being ...
Pusher
What's new in control groups (cgroups) version 2?
Michael Kerrisk https://2019.linux.conf.au/schedule/presentation/124/ Control groups (cgroups) version 1 was released in 2008, and within a short time people ...
linux.conf.au
How to set up a direct interconnection between Azure and Oracle Cloud Infrastructure | Azure Friday
Romit Girdhar (Microsoft) and Chinmay Joshi (Oracle) join Lara Rubbelke to explain how to interconnect Microsoft Azure and Oracle Cloud Infrastructure.
Microsoft Azure
Dive Deep Into RDS New Features - AWS Online Tech Talks
Amazon Relational Database Service (Amazon RDS) is a fully managed database service that allows you to launch an optimally configured, secure, and highly ...
AWS Online Tech Talks
CI/CD Pipeline Security: Advanced Continuous Delivery Best Practices
Continuous delivery (CD) enables teams to be more agile and quickens the pace of innovation. Too often, however, teams adopt CD without putting the right ...
Amazon Web Services
Software Testing Tutorial For Beginners | Software Testing Automation Tutorial | DevOps |Simplilearn
This Software testing tutorial covers the basics of software testing and the automation tools used for software testing. We'll look at the test-driven development ...
Simplilearn
Azure Monitor action groups | Azure Friday
Azure Monitor action groups enable you to define a list of actions to execute when an alert is triggered. In this episode, we demonstrate how to configure a ...
Microsoft Developer
Detecting Threats in Logs at Cloud Scale (Cloud Next '19)
Google has protected its corporate and production environments by analyzing logs for over a decade. In this talk, we'll give an overview of how Event Threat ...
Google Cloud
SQL Server 2017 Always On Availability Groups – WINDOWS AND LINUX DEPLOYMENTS
Introduced in SQL Server 2012, Always On Availability Groups maximizes the readiness of a set of user databases as an availability group that can fail over as a ...
High Availability Disaster Recovery Virtual Group
Microsoft Defender ATP architecture
This video describes the architecture of Microsoft Defender Advanced Threat Protection. Try Microsoft Defender ATP for free or request a quote: ...
Microsoft 365
Installing a Cisco Unity Connection (CUC) 12.0 Server
===================================================== In this video, you'll learn how to install the Cisco Unity Connection (CUC) 12.0 Server, ...
Kevin Wallace Training, LLC
The Definitive Guide to Hosted UniFi
The Definitive Guide to Hosted UniFi is a living document that details best practices for setting up and securing a hosted UniFi Controller. Full written instructions: ...
Crosstalk Solutions
Edward Witten: On the Shoulders of Giants
Acknowledging the scientists who blazed intellectual trails before him, Isaac Newton wrote, “If I have seen a little further it was by standing on the shoulders of ...
World Science Festival
Conditional Access in Enterprise Mobility + Security
Microsoft engineer and identity expert Alex Simons, joins Simon May to demonstrate updates to Conditional Access, part of Microsoft's Enterprise Mobility + ...
Microsoft Mechanics
Linux Server Build: OpenVPN From Scratch - Hak5 2019
apt-get update; apt-get install openvpn easy-rsa gunzip -c /usr/share/doc/openvpn/examples/sample-config-files/server.conf.gz /etc/openvpn/server.conf nano ...
Hak5
Introduction to Red Hat 3Scale (DO040)
Red Hat Agile Integration Technical Overview (DO040) provides a technical introduction to Red Hat's comprehensive set of integration and messaging ...
Red Hat
Securing your data in SharePoint/OneDrive/Microsoft Teams with Sensitivity Labels
In this 45-minute administrator/developer focused tour of the latest security controls and sensitivity labeling capabilities available today or soon in SharePoint, ...
Microsoft 365 Community
Introducing Multi-Geo capabilities in Office 365 and how to configure them
See the capabilities of Multi-Geo in Office 365 which allows you to determine, where your data resides within a single Office 365 tenant across multiple regions ...
Microsoft Mechanics
Advanced Zeek Usage Scripting and Framework
The open-source Network Security Monitor (NSM) and analytics platform Zeek (formerly known as Bro) became well-known in the information security industry ...
SANS Digital Forensics and Incident Response
Public Key Infrastructure Fundamentals - Bart Preneel
The function of a public key infrastructure (PKI) is to ensure secure delivery and management of public keys. Alternative trust models lead to different key ...
secappdev.org
VMware NSX Edge Gateway & Distributed Firewall with Tim Davis @aldtd #vBrownBag
Tim Davis wraps up the mini NSX ninja series discussing Edge Gateways (ESG) and Distributed Firewall (DFW). Show Notes *About vBrownBag* - Edge ...
vBrownBag
UniGUI Web App Development
uniGUI Web Application Framework extends Web application development experience to a new dimension. uniGUI enables developers to create, design and ...
Embarcadero Technologies
Kubernetes Full Course | Kubernetes Architecture | Kubernetes Tutorial For Beginners | Simplilearn
In this full course video on Kubernetes, you have a brief introduction of Kubernetes and then learn how to install Kubernetes on Ubuntu. Then, we dive deep into ...
Simplilearn
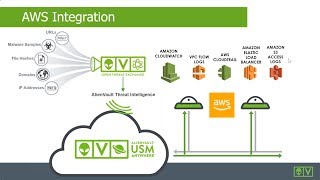
How to Achieve PCI DSS Compliance on AWS
USM Anywhere from AlienVault provides a comprehensive threat detection and compliance solution for monitoring cloud and on-premises environments.
Amazon Web Services
Dell EMC Unity Product Overview and Architecture with Kaushik Ghosh
Kaushik Ghosh, Senior Management, Product Development with Dell EMC Unity, gives a product overview of their line. This includes their all-flash arrays, ...
Tech Field Day
Coronavirus: LAUSD superintendent warns of consequences of diminished funding due to pandemic
Update: In his weekly briefing on May 18, LAUSD Superintendent Austin Beutner discussed how state budget cuts caused by the COVID-19 outbreak could ...
KTLA 5
Security configuration in Microsoft Defender ATP
Microsoft Endpoint Manager is a central place to manage the configuration of organizations' devices. In this video, you'll learn how to use it to manage security ...
Microsoft 365
Let's Encrypt UniFi
How to install a Let's Encrypt certificate on UniFi and configure crontab to automatically renew the certificate every 12 hours. 15 Minute Hosted UniFi Controller: ...
Crosstalk Solutions
Azure Information Protection Demo
Azure Information Protection (End User Adoption Guide), https://goo.gl/iqGH4h Install AADRM PowerShell Module, https://goo.gl/CRcAUN.
Atul Raizada
Technical Monitoring with SAP Solution Manager 7.2
Reduce downtime and monitor your SAP applications from anywhere In this webinar workshop, we learn how SAP Solution Manager 7.2 helps minimize ...
CoreALM
Обзор подсистемы Автосервис конфигурации "МВС: Детали машин" - Часть 1/4
Первая часть из четырех видео обзора подсистемы Автосервис конфигурации "МВС: Детали машин". Обзор состоит из четырех частей: Часть первая ...
MBCGroupRU
Untangle 101: Untangle at Home
Concerned about getting visibility into your home network? Disappointed with the functionality of your Wi-Fi router? Consider running Untangle with our ...
Untangle, Inc.
Citrix Synergy TV - SYN229 - nFactor and Login Schemas...
Citrix Synergy TV - SYN229 - nFactor and Login Schemas: the future of NetScaler customization With earlier versions of NetScaler firmware, administrators ...
Citrix
OctopusPro Demo - Contractor Field Service Management Software
OctopusPro Field Service Management (FSM) software enables businesses to manage all aspects of their field service and site based operations. This demo ...
OctopusPro
Oracle Database 18c New Security Features
Held on August 9 2018 In this AskTOM session Russ Lowenthal focuses on new security features in Oracle Database 18.3 - recently released for on-premises ...
Oracle Developers