Conditional Access in Enterprise Mobility + Security
Microsoft engineer and identity expert Alex Simons, joins Simon May to demonstrate updates to Conditional Access, part of Microsoft's Enterprise Mobility + ...
Microsoft Mechanics
GOTO 2016 • Phoenix a Web Framework for the New Web • José Valim
This presentation was recorded at GOTO Copenhagen 2016 http://gotocph.com José Valim - Creator of the Elixir programming language and co-founder of ...
GOTO Conferences
SYN328 - Federated Authentication Service, SAML with XenApp and XenDesktop
New in XenApp and XenDesktop 7.8, Federated Authentication Service enables authentication from worlds outside the username/password/smartcard set ...
Citrix
Dynamics 365 Customer Voice overview
Customer Voice is an enterprise feedback management solution that empowers organizations to capture customer feedback directly from surveys personalized ...
Microsoft Dynamics 365
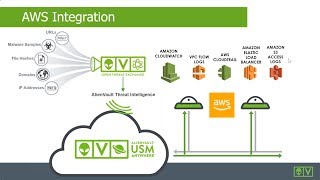
How to Achieve PCI DSS Compliance on AWS
Learn more about the AWS Partner Webinar Series at - http://amzn.to/2iT0zvA AWS offers extensive logging capabilities with services including Amazon Simple ...
Amazon Web Services
Early look at Microsoft Threat Protection
Microsoft Threat Protection harnesses trillions of threat signals from the Microsoft Intelligent Security Graph to secure your workplace using Microsoft Threat ...
Microsoft Mechanics
Network protection in Microsoft Defender ATP
Network protection helps reduce the attack surface of your devices from Internet-based events. It prevents employees from using any application to access ...
Microsoft 365
Security configuration in Microsoft Defender ATP
Microsoft Endpoint Manager is a central place to manage the configuration of organizations' devices. In this video, you'll learn how to use it to manage security ...
Microsoft 365
NetScaler Master Class August 2018
Welcome to the Citrix NetScaler Master Class. Get details on latest features of NetScaler, tips and tricks for easy configuration, and interact with our NetScaler ...
Citrix
Advanced Zeek Usage Scripting and Framework
The open-source Network Security Monitor (NSM) and analytics platform Zeek (formerly known as Bro) became well-known in the information security industry ...
SANS Digital Forensics and Incident Response
Coronavirus: LAUSD superintendent warns of consequences of diminished funding due to pandemic
Update: In his weekly briefing on May 18, LAUSD Superintendent Austin Beutner discussed how state budget cuts caused by the COVID-19 outbreak could ...
KTLA 5
Introduction to jBPM | jBPM Components | jBPM Architecture | jBPM Tutorial | Intellipaat
Intellipaat jBPM course: https://intellipaat.com/jbpm-drools-training/ In this jBPM tutorial video you will learn the basic introduction to jBPM, the jBPM components, ...
Intellipaat
Advanced hunting in Microsoft Defender ATP
Advanced hunting is a query-based threat-hunting tool that lets you explore up to 30 days of raw data. You can proactively inspect events in your network to ...
Microsoft 365
An Overview of Designing Microservices - March 2017 AWS Online Tech Talks
Microservices are an architectural approach to decompose complex applications into smaller, independent services. AWS customers benefit from increased ...
AWS Online Tech Talks
Advanced Data Security with Azure SQL Database in Azure Government
In this episode of the Azure Government video series, Steve Michelotti sits down to talk with Ajay Jagannathan of the Azure SQL Database Engineering team, ...
Microsoft Azure
Technical Monitoring with SAP Solution Manager 7.2
To learn more about SAP Solution Manager, visit us: http://bit.ly/2njGdk8 Reduce downtime and monitor your SAP applications from anywhere In this webinar ...
CoreALM
AWS re:Invent 2018: Build a Hybrid Cloud Architecture Using AWS Landing Zones (ENT304-R1)
Application modernization projects with AWS start with creating an AWS Landing Zone. Based on AWS best practices, AWS Landing Zones help ensure a ...
Amazon Web Services
Manage User Privileges on Your Synology NAS | Synology
With DSM's granular user management options, you can delegate privileges for users/groups, manage shared folder access permissions, storage/shared folder ...
Synology
UniFi SSL Certificate Installation
Do you have a Debian or Ubuntu based UniFi controller? Do you want to put a CA signed SSL certificate on it? You should! Follow these instructions to get up ...
Willie Howe
Kubernetes Full Course | Kubernetes Architecture | Kubernetes Tutorial For Beginners | Simplilearn
In this full course video on Kubernetes, you have a brief introduction of Kubernetes and then learn how to install Kubernetes on Ubuntu. Then, we dive deep into ...
Simplilearn
Security Best Practices for Serverless Applications - 2017 AWS Online Tech Talks
Learning Objectives: - Learn security best practices for AWS Lambda and Amazon API Gateway - Understand how to use Amazon Cognito to build identity and ...
AWS Online Tech Talks
UniFi Guest Network with Captive Portal
This is a LONG video, and a bit different than my normal videos. You will see me set up an actual client's wireless guest network and captive portal in real time, ...
Crosstalk Solutions
Build a Company in Azure
Welcome to “Build a Company in a Azure” a session packed with demonstrations that show you just how easy it is to build solutions in the Microsoft Cloud.
Daniel Baker
DjangoCon US 2015 - Managing Identities: LDAP, Google Directory, and Django by Scott Hacker
Managing Identities: LDAP, Google Directory, and Django Universities and other enterprises often deploy a complex mix of systems for managing identities and ...
Confreaks
AZ-900 Episode 8 | Resources, Resource Groups & Resource Manager | Azure Fundamentals Course
Microsoft Azure Fundamental full course. Episode covers following skills - Describe Resources - Describe Resource Groups - Describe Resource Manager ...
Adam Marczak - Azure for Everyone
Meet compliance and manage risk with Advanced Data Governance
Data is growing in volume and variety in today's modern workplace. Learn how simple, integrated and intelligent data governance in Microsoft 365 can help you ...
Microsoft 365
Top New Features in FortiClient EMS 6.0
Explore FortiClient Next-Generation Endpoint Protection: https://www.fortinet.com/products/endpoint-security/forticlient.html See how FortiClient strengthens ...
Fortinet
System Administration—Migrating from Avaya Site Administration to System Manager
Avaya is making moves toward System Manager as the central point of administration for the various Aura applications. System Manger's capabilities far surpass ...
ASI is now ConvergeOne
Baron Antonie-Henri Jomini, Theories of War
Dr. Bill Johnsen, Prof. Mil History and Strategy, USAWC, Sep. 6, 2017.
USArmyWarCollege
Production UniFi Upgrade
This video shows a real world example of the actual process for upgrading a production UniFi Controller that is hosted on Amazon AWS. When working in ...
Crosstalk Solutions
Public Key Infrastructure Fundamentals - Bart Preneel
The function of a public key infrastructure (PKI) is to ensure secure delivery and management of public keys. Alternative trust models lead to different key ...
secappdev.org
How to configure an Auto-Attendant with CUC 11.x
In this video, learn how to configure a basic Auto-Attendant with CUC 11.x, this is applicable for any previous versions as the config elements are the same.
Cisco Community
15 Minute Hosted UniFi Controller Setup
How to set up a UniFi Controller on a Digital Ocean Droplet in about 15 minutes. Digital Ocean referral link: https://m.do.co/c/6de2bc2df3b8 Full text instructions ...
Crosstalk Solutions
Throw Me a Lifebuoy: Debugging Node.js in Production with Diagnostic Reports - Christopher Hiller
Christopher Hiller, IBM Diagnostic Reports are a recent addition to Node.js core. This feature enables insight into Node.js processes running in ...
node.js
January 2021 Current affairs in English | GKToday
January 2021 Current affairs in English GKToday | Daily current affairs 2021 in English GK Today daily current affairs in English are based on GKToday's ...
GKToday
Getting Started with Serverless Architectures
Serverless architectures let you build and deploy applications and services with infrastructure resources that require zero administration. In the past, you had to ...
Amazon Web Services
Firepower Management Center Migration Tool
The new ASA to FTD configuration migration tool in Firepower Management Center enables existing ASA or ASA with FirePOWER services customers to migrate ...
Cisco
Advanced Techniques for Federation of the AWS Management Console and Command Line Interface (CLI)
Learning Objectives: - Enable users to sign into the AWS Management Console and AWS CLI using AD or SSO credentials - Manage user access to AWS using ...
AWS Online Tech Talks
SolarWinds Log and Event Manager Technical Overview
Rob Johnson, Product Marketing Manager, introduces SolarWinds Log and Event Manager (LEM) and provides a demonstration of the network and security ...
Tech Field Day
Office 365 Groups – Overview & Administration
Microsoft Office 365 Groups helps you collaborate by easily bringing together your colleagues and the applications you need to get work done. Office 365 ...
Microsoft Tech Summit
Dynamics 365 Essentials for IT | Intro
An explanation of the Dynamics 365 components, underlying architecture, and the possible integrations with your existing data, apps, and business processes.
Microsoft Mechanics
Anthony Scopatz - xonsh - PyCon 2016
Speaker: Anthony Scopatz Xonsh is general purpose shell that combines Python and the best features of Bash, zsh, and fish. Relying only the standard library ...
PyCon 2016
![[Справочник единых норм времени] : Слесарный ремонт бурового оборудования и инструмента : Дополнения и изменения... : Утв. в 1951 г](https://static.rusist.info/screens/008/201/773.jpg)